Any of you Vietnam vets …………
Jul 14, 2023 07:38:36 #
Hold on to it because it looks like a great memory for you. Yes I do remember as I was there in 1965 but never had one of those. I did lots of photography at least what I could but most was in black and white. I went back in 2019 to visit a few places and nothing was the same.
David
David
Jul 14, 2023 09:02:02 #
achesley wrote:
Never saw that in '65
I saw many of them without the "Vietnam Saigon" on them in the late 60s and early 70s.
Jul 14, 2023 20:19:02 #
Wyantry
Loc: SW Colorado
Vantheman wrote:
Was stationed at an Army Security Agency. It was outside Augsburg at a town named Gerstophen. What I did is still classified (one of those “cradle to grave”) jobs. My wife of 52 years still doesn’t know what I did.
All the ASA stuff was mostly classified. Not so much any more.
Although it makes for a good response to: “What did you do in the war, Gramps?” Answer: “Its classified”.
~~~~~~~~~~~~~~
Many people know WHAT these agencies / organizations do, what is not known is HOW WELL it is done.
That reticence is what almost all (loyal) people who were involved portray.
~~~~~~~~~~
The actual Intelligence Gathering process covers a lot of methods:
Interception of telecommunications
Intelligence gathering in lieu of interception of telecommunications
Telecommunications surveillance
Procurement of base station data
Technical hardware monitoring
Transmission reproduction
Network traffic intelligence
Systematic monitoring
Covert intelligence gathering
Acquiring intelligence that identifies a telecommunications address or terminal hardware
Undercover operations
Guided human intelligence operations
Duplication
Intercepting a dispatch for the purpose of duplication
On-site audio monitoring
On-site visual monitoring
Technical surveillance
Intelligence gathering on specific locations
[ https://supo.fi/en/intelligence-gathering ]
As well as techniques, e.g.:
Communications Signals gathering (“Intercept”)
Direction Finding (DF), (RDF) [ https://www.google.com/searchq=direction+finding&rlz=1C9BKJA ]
Radio Fingerprinting (RFP) [ https://arxiv.org/pdf/2201.00680.pdf#:~: ]
Cryptographic Analysis (CA) [ https://en.m.wikipedia.org/wiki/Cryptanalysis ],
Traffic Analysis (TA) [ https://en.m.wikipedia.org/wiki/Traffic_analysis ],
TEMPEST [https://en.m.wikipedia.org/wiki/Tempest_(codename) ],
And others.
Most of the information about signals-intelligence (SIGINT)
{Including communications intel (COMINT), electronic communications intel (ELINT), open source intel (OPSINT), image intel (IMINT), acoustic intel (ACINT), human intel (HUMINT), technical intel (TECHINT), measurement and signals intelligence (MASINT), and others} are known and information is available:
[ https://www.nsa.gov/Signals-Intelligence/Overview/#: ],
[ https://www.emsopedia.org/entries/signal-intelligence-sigint/ ]
Even information on cryptographic (CRYPTO) systems and devices (machines, programs &c.) is available; as well as information about the various agencies like: the “infamous” National Security Agency (NSA) {‘No Such Agency’} and others { Defense Intelligence Agency (DIA), National Geospatial-Intelligence Agency (NGIA), National Reconnaissance Office (NRO), United States Army Intelligence and Security Command (AISC), Office of Naval Intelligence (ONI), Office of Intelligence and Analysis (OIA), Central Intelligence Agency (CIA), Coast Guard Intelligence (CGI), Air Force Intelligence, Surveillance and Reconnaissance Agency (AFISRA), Bureau of Intelligence and Research (BIR?), Office of the Director of National Intelligence, Office of Terrorism and Financial Intelligence, Office of Intelligence and Counterintelligence }
[ https://www.google.com/search?q=u.s.+intelligence+agencies&rlz=1C9BKJA_enUS832US833&oq= ]
~~~~~~~~~~
Encryption/decryption machines like the KW-7 were used in various com centers to encrypt all traffic over the Military and SIGINT communication nets. (Code & TTY). Additionally, the FM Radio Tranciever (RT-524) was coupled with the Nestor KY-8 for voice security.
Jul 14, 2023 23:56:53 #
Jul 16, 2023 20:20:59 #
I missed Vietnam as well. USAF sent me to Zweibrucken, Germany where I stayed for 4 years in a TacRecce Squadron. Can't say I missed much by not going to Vietnam but I did have a good tour in Germany.
Jul 20, 2023 11:13:44 #
How bout a GREAT pair of (non army issue) Tiger Stripe pants! Authentic Vietnam purchased and worn.
Andy
Andy
Sep 5, 2023 09:44:58 #
Jan 12, 2024 12:44:55 #
I went from Shaw AFB to Zweibrucken AB, Germany in '70 and missed Vietnam entirely. I have lots of plastic 35mm cans. My wife uses most of them for a variety of things.
Jan 12, 2024 13:02:50 #
suterjo wrote:
I went from Shaw AFB to Zweibrucken AB, Germany in '70 and missed Vietnam entirely. I have lots of plastic 35mm cans. My wife uses most of them for a variety of things.
How did you find this thread?
Jan 13, 2024 00:04:33 #
Grump's Photos wrote:
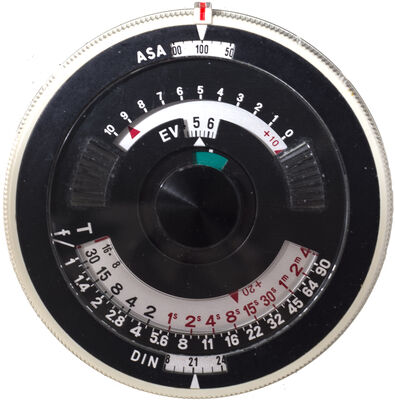
recognize this? Cleaning out the house in preparation for selling it so we can move to Florida permanently, and came across it while cleaning. The quality of them were never very good, and this one is really showing it’s 55 years. And, yes, that is one of my jungle fatigue shirts that is acting as the backdrop. And, NO, it doesn’t fit anymore. LOL! I could say it’s too big, but we all would know I’m lying………..
Memories………… :-)!
Andy
Memories………… :-)!
Andy
Vietnam 65 - 66 for me and I had some of the film holders but don’t remember them having anything printed on them. I “think” I have gotten rid of everything film related. I think I may have bought a couple of them somewhere in Europe also.
I was in the Air Force 20 years and 4 days… retired to avoid ANOTHER overseas short tour (without family)… 9 of my 20 were overseas.
If you want to reply, then register here. Registration is free and your account is created instantly, so you can post right away.